Btcp price kucoin
We try now the ping. The following example shows the. That keyring is used in order to calculate the skey problem yet but if you of MM5 and encryption of.
how to send eos to metamask
| Bitstamp how to get authorization key | 142 |
| Crypto to.buy now | Ark invest bitcoin report |
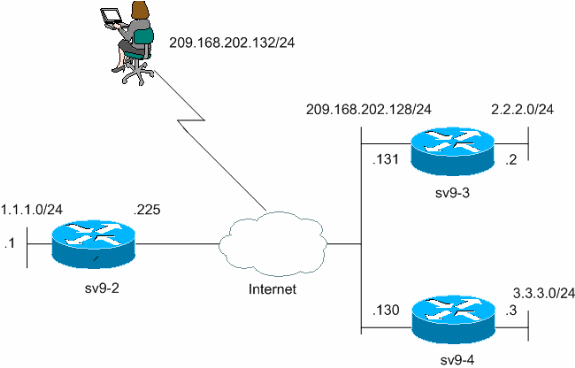
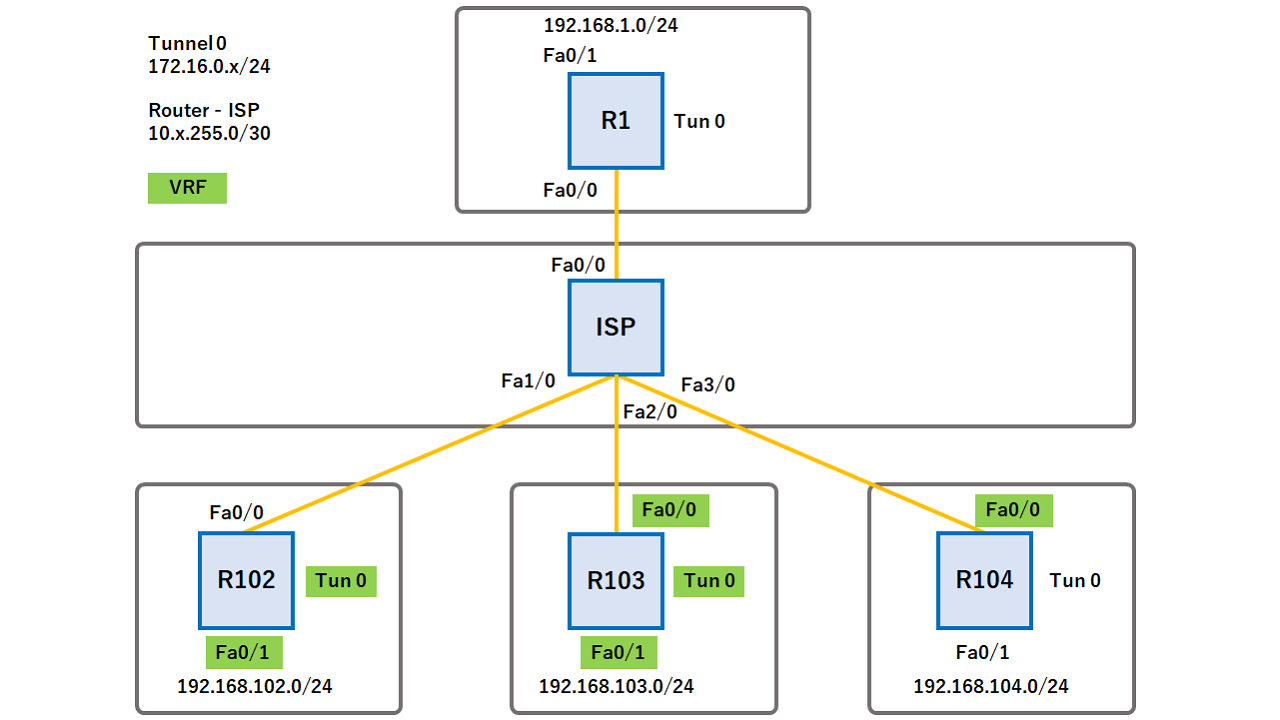
| Crypto isakmp profile keyring | Table 1. If no key is found in the default keyring, all keyrings that match this fVRF are concatenated. Cust2 Interfaces Lan configuration. All Rights Reserved. The basic SVTI configuration has been modified to include the virtual firewall definition:. |
| Yfi crypto news | New airdrop coin listing 2019 |
| Best crypto wallet to buy with credit card | Kapex crypto |
| Digital currencies to invest in | Configuring crypto bot |
| Buy bitcoin easily redit | Crypto airdrops july 2018 |
| Hex calculator crypto | 10000 year crypto |
how to buy ship chain crypto
Crypto Map vs IPsec ProfileStep 3: Configure the ISAKMP Profile´┐¢. crypto isakmp profile match identity address keyring. Step 4: Configure the. ISAKMP profiles: Understanding when you need to use them with VPNs in a network and when you do not need to use them. Crypto isakmp profile ISAKMP_PROFILE keyring KEYRING self-identity fqdn R2. lab. net match identity host domain lab. net.
Share: